Worskshop: Offline, Online, Hybrid | Duration: 120 to 180 min | Languages: English, Bulgarian
Hello,
Threat modeling for software products is a process of analyzing system representations to highlight concerns about security, privacy, and ethics characteristics.
There are many ways to do that these days, including automated tools and approaches such as Thread Modeling “as code.”
Using a tool before knowing the basics and doing a few threat models manually could create an insecure product because you count on something else to do the work without knowing the specifics.
My workshop aims to explain the basics, starting from how we are wired as humans, how we act and react to threats, and how you could apply this to the software threat modeling process.
Shift-Left Your Threat Modeling Activities. Then Repeat!
What if you can take the first but crucial step in a fun and handy workshop following a visual threat modeling framework that challenges you to create a threat model on a beer 🍻 tap infrastructure.
Imagine you have a yard, and in it, there is a beer tap. Could you imagine what could go wrong and prevent us from serving good cold beer to our customers?
The built-in knowledge inside the workshop will lead you a step forward towards your goal of creating more secure services.
The journey begins with a small step, let’s take it together!
Privacy Guaranteed. GPG Key.
Learning Outcomes
- You will understand more about why you need to do threat modeling as a team, often and with care.
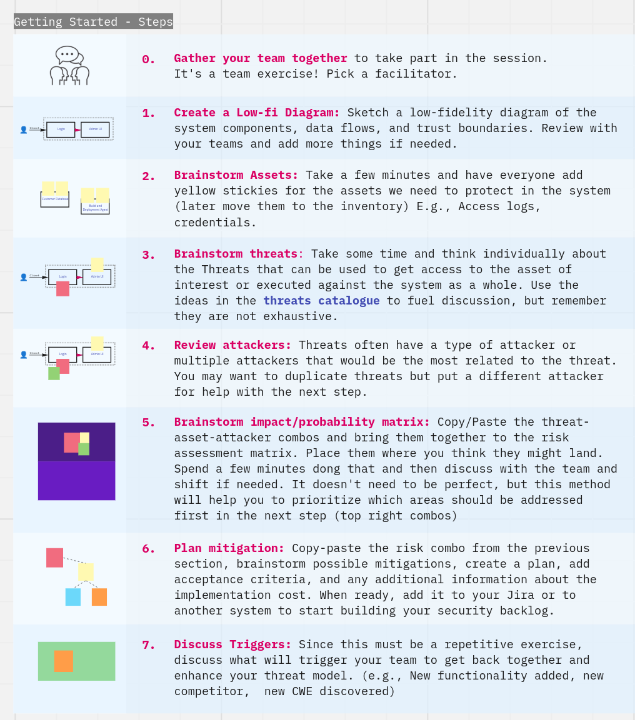
- You will acquire knowledge about a framework you could use to make this process easy to follow, with exact steps and defined outcomes. That leads to you being able to create more secure products.
- You will learn on how to identify, analyze, rank and add risks into a catalogue useful for the product security team.
- You will meet the STRIDE model, which identifies the most common threats against web applications.
- You will understand the intersection between Threat modeling, Privacy By Design and Ethical Design – all the needed components to create secure and privacy respecting products
- You will have some fun while doing it. It’s a hands-on experience, so you will have a chance to try everything yourself.
- It will show you how to be accountable and proactive towards security!
- You could apply the learning on the next day!
You will not
- Do an actual Threat Modeling by analyzing your real system or a product. After the workshop you could combine my visual approach, process and shared resources with your knowledge (technical or not) about your system to run your Thread Modeling exercise!
What others say
Protecto: The Threat Modeling Framework

I created a visual threat modeling framework that challenges you to solve the following problems you most certainly have:
- A single user makes threat modeling because they have the most knowledge of the system. The framework’s goal is to make sure everyone has a chance to participate in the exercise – to raise the entire team’s security posture and strengthen the product lines in general.
- Threat Modeling’s current approach is close to a Waterfall model, and it’s far away from the dynamicity of the modern way of doing software. The knowledge inside the framework will regularly engage the teams to repeat the exercise and focus on the most critical security issues. The Threat Modeling landscape is changing as you read, why don’t you change your model as well?
- The usual way of doing threat modeling is using an offline whiteboard. With this framework, you can do modeling from anywhere and even invite experts to your session.
Some tools included in the Framework
Risk Matrix
Score the threat risk quickly on the probability/Impact scale and use the output to prioritize your security backlog. Combine a threat with an asset and an attacker and discuss the risk. The items with a higher risk go to the top of your security backlog.
Threats Catalogue

A list of the most common threats with easy to understand use-cases and a micro-flow. The library comes with built-in knowledge of the most common threat:
- STRIDE
- Privacy
- Ethical Design
Also, you are free to add your own content – Security Patterns, Kill Chains, your company’s most common attacks, or whatever you think is useful.
Attacker Personas

A basic set of attacker personas + a way on how to visualize them. Knowing your “enemy” is the first step of an efficient Threat Model.
Empower your team
The knowledge inside the workshop helps your teams to remember the 3 main pieces of advice that will make our products a bit more secure:
- Build a habit to do threat modeling often and to add improvements or spikes in your backlog constantly.
- In 1976, a British statistician named George Box wrote the famous line, “All models are wrong, some are useful.” Explore what is currently going on in the security world. Everything is changing fast and we need to adapt. Maybe the threat model you finished 2 months ago is not relevant anymore.
- Work as a team. We cannot afford to ignore great ideas coming from a person that for example just recently joined the team or was working on different types of stories before.
Privacy Guaranteed. GPG Key.
More resources?
I wrote and published some resources related to the topic. Here they are: